Many companies in Germany urgently need to take action: the NIS2 Implementation Act entered into force in December 2025, transposing the EU’s cybersecurity directive into German federal law. Affected companies must now demonstrably meet higher IT and information security requirements – or face significant penalties for non-compliance. LHIND can assist you with comprehensive NIS2 consulting and compliant implementation of all required measures. Our services range from conducting impact analyses to implementing suitable measures and demonstrating compliance to the Federal Office for Information Security (BSI).
NIS2 Consultancy: German Implementation Act Increases Cybersecurity Requirements – Is Your Company Affected?
What is the NIS2 Implementation Act?
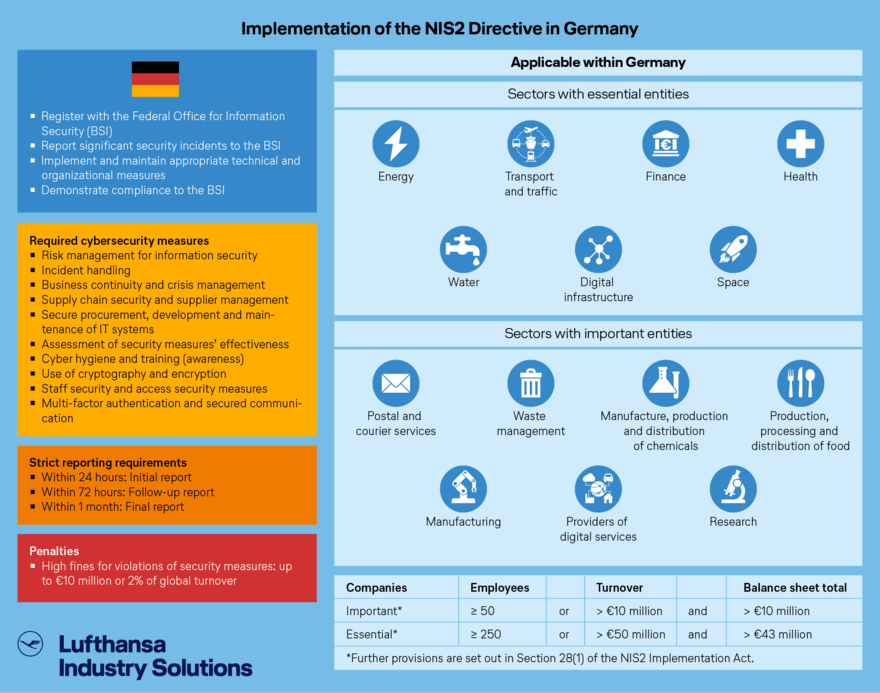
The NIS2 Implementation Act (NIS2-Umsetzungsgesetz) is a piece of federal legislation that transposes the provisions of Directive (EU) 2022/2555 on network and information security (NIS) into German law. It replaces the previous NIS regulations from 2016 and significantly expands the scope of application with more stringent security requirements, additional sectors and a larger number of affected companies.
The German law came into force on December 6, 2025. The affected companies – and particularly those in essential and important areas as defined by the EU directive – are required to register with the Federal Office for Information Security (BSI), report significant security incidents, and implement and demonstrate operation of appropriate technical and organizational security measures.
The affected companies must register with the BSI by March 6, 2026. Evidence of compliance must be provided on a regular basis. Otherwise, companies face significant penalties of up to €10 million or 2% of their global turnover, depending on their classification and degree of criticality.
Don’t let it get that far – Lufthansa Industry Solutions (LHIND) can support you with NIS2 consulting services, helping you establish fully compliant risk management for improved cybersecurity!
How Can LHIND Help Your Company Implement NIS2 Requirements?
Our IT security experts can advise you on all NIS2-related issues and help you to implement the new requirements as effectively as possible. We have years of experience in supporting companies related to critical infrastructure – known in Germany by the abbreviation “KRITIS” – and would be happy to assist you as a skilled and reliable partner.
The ideal way to determine your NIS2 readiness and needs
Are you still lacking a precise overview of how ready your company is for the NIS2 Directive? Would you benefit from insights into outstanding tasks?
Our NIS2 consulting services are the ideal way to get started. We provide transparency and an overview of the areas in need of optimization.
Request a non-binding assessment
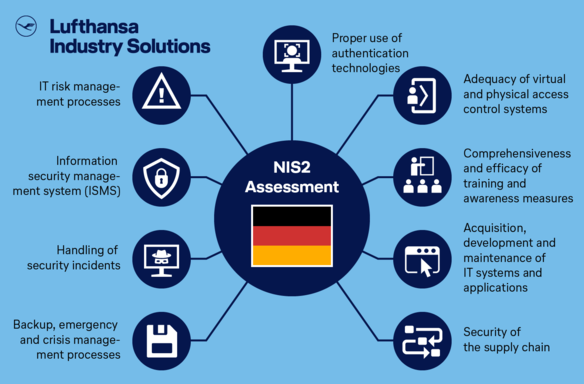
With regard to the NIS2 requirements, we examine:
- Your IT risk management processes
- Your information security management system (ISMS)
- How you deal with security incidents
- Your backup, emergency and crisis management processes
- The security of your supply chain
- How you acquire, develop and maintain your IT systems and applications
- The comprehensiveness and effectiveness of your training and awareness measures
- The adequacy of your virtual and physical access control systems
- Proper use of authentication technologies in your company
We also offer:
- Implementing and reviewing necessary measures, such as set-up and optimization of risk management, reporting and notification channels, incident management, business continuity management, supplier and customer management, and other measures
- Reviewing the implementation of measures in accordance with the law’s requirements
- Performing penetration tests to detect acute technical vulnerabilities (optional)
- Standards-compliant consulting on setting up and implementing IT risk management and ISMS structures
- Independent auditing of IT risk management and ISMS
- Setting up effective detection and response processes
- Supporting incident handling
- Setting up rules and technical structures
- Conducting emergency simulations and exercises
- Identifying information flows and data classification
- Coordinating comprehensive security requirements
- Securing professional and technical interfaces
- Setting up and controlling provider management
- Migrating systems to effective platforms
- Management training
- Raising employee awareness and providing training
- Measuring and optimizing the awareness level
- Providing professional and technical advice on potential solutions
- Implementing potential logical and physical solutions
- Securing audio, video and text communications
- Setting up emergency communications systems
We’re here to assist as your reliable expert partner. Here’s what sets us apart:
- Many years of experience in the IT security and information security sectors, and in consulting companies related to critical infrastructure (KRITIS)
- Expertise in data protection, compliance, information security and the technical IT sector
- In-depth industry knowledge of optimal solutions in different customer situations
- Tailored solutions for your individual requirements
- Rapid and individualized adaptation to your needs as well as comprehensive flexibility
- Qualified all-around support from analysis to implementation and quality control
- A comprehensive service package, regardless of your company’s size
Which Companies are Affected by the NIS2 Implementation Act?
The NIS2 Implementation Act covers various sectors, which it classifies as “essential” or “important”:
| Essential entities | Important entities |
|
|
| Penalties for violations: Maximum amount of €10 million or 2% of global turnover (whichever is higher) | Penalties for violations: Maximum amount of €7 million or 1.4% of global turnover (whichever is higher) |
Company Size is also a Factor in NIS2 Coverage
The NIS2 Implementation Act applies the size-cap rule, which means it primarily affects medium-sized and large enterprises in the affected sectors.
| Company | Employees | Turnover | Balance sheet total | ||
| Important* | ≥ 50 | or | > €10 million | and | > €10 million |
| Essential | ≥ 250 | or | > €50 million | and | > €43 million |
*Further provisions are set out in Section 28(1) of the NIS2 Implementation Act.
However, smaller enterprises may also be affected if they
- perform a critical activity,
- have an impact on public order, or
- are subject to systemic risks with potential cross-border impacts.
Nevertheless, a company may be fully exempted from the NIS2 Implementation Act under certain circumstances, even if they operate in an affected sector.
NIS2 Implementation: What Your Company Needs to Do
The German NIS2 Implementation Act came into force in December 2025. Consequently, the obligations for affected companies are now binding and in full effect. Here’s what companies need to do:
- Check whether they are affected by the law (based on their sector, size and criticality)
- Register with the BSI by the legally specified deadline (by March 6, 2026)
- Implement appropriate technical and organizational measures (TOMs)
- Introduce functional reporting processes for security incidents (24 hours / 72 hours / 1 month)
- Prepare to demonstrate compliance to the BSI (audits, reports, certification if applicable)
There is no transition phase. Companies must act now to avoid compliance risks, fines and management liability.
Take advantage of our NIS2 consulting
NIS2 Requirements and Associated Measures
Companies classified as essential or important entities under the NIS2 Implementation Act are subject to binding legal obligations – from registering with the BSI to implementing a range of security measures. These measures must be guided by the company’s specific risk situation, the criticality of its services and the latest technological developments. For many companies, these elevated security requirements represent a significant organizational and technical adjustment.
The measures must be based on a holistic approach to risk management and, in addition to cyberattacks, take account of technical, organizational and physical risks. The aim is to provide IT systems, processes and the provision of affected services with effective protection against disruption and outages. In addition, management teams must regularly participate in training courses on risks and risk management practices.
The law’s expanded scope means that many organizations will need to significantly upgrade their network monitoring, incident response capabilities and security structures.
Fully compliant risk management in line with the NIS2 Implementation Act
The NIS2 Implementation Act requires essential and important entities to introduce and maintain an appropriate, risk-based information security and risk management system. The legal minimum requirements include in particular:
- Risk analysis and security guidelines
Establish guidelines and procedures to manage information security risks - Incident management
Prevent, identify, manage and investigate security incidents - Business continuity management (BCM)
Measures to uphold business operations, including back-up, disaster recovery and crisis management measures - Supply chain security
Risk management for service providers, suppliers and partners, including secure development and operating processes - Secure procurement, development and maintenance
Security requirements for IT and network systems, vulnerability management and coordinated disclosure - Assessment of security measures’ effectiveness
Regular reviews, testing and improvement of protective measures - Cyber hygiene and training
Raising employees’ awareness and holding regular training - Cryptography and encryption
Protecting data in non-operating state and during transmission - Personal and physical security
Access controls, authorization management and protection of IT assets - Secure authentication and communication
Use of strong authentication procedures (e.g. MFA) and secured voice, video and data communication, including emergency communication
Supply chain requirements for NIS2 implementation in Germany
Securing supply chains for goods and services is a core component of the law. In addition to their own systems, companies are also required to consider their reliance on external service providers and suppliers.
This includes in particular:
- Taking account of cyber risks in the context of service provider selection and management
- Defining security requirements in contracts
- Assessing risks arising from the development, operation and maintenance of external systems
The intensified requirements are a response to the growing threat posed by supply chain attacks, in which attackers exploit compromised suppliers to gain access to customer and partner networks.
Reporting security incidents to the BSI
The NIS2 Implementation Act sets out binding requirements for reporting to the Federal Office for Information Security (BSI). Companies must establish suitable processes to comply with the reporting periods:
- Within 24 hours: Initial report of a significant security incident
- Within 72 hours: Qualified report, including an assessment and indicators of compromise (IOCs)
- Within 1 month: Final report, including causal analysis and remedial measures
For many companies, these legal requirements mean an increased organizational, technical and administrative workload, especially in relation to incident response, documentation and governance.
FAQ: Important questions about the NIS2 Directive
Failure to meet the requirements of the NIS2 Implementation Act may be punished with significant fines of
- up to €10 million or
- up to 2% of global annual turnover,
plus instigation of proceedings under regulatory law by the BSI. In addition, company management risk being held personally liable.
The NIS2 Implementation Act (NIS2-Umsetzungsgesetz) is a piece of federal legislation that transposes the provisions of Directive (EU) 2022/2555 into German law. It replaces the existing NIS regulations and significantly increases both the number of affected companies and the network and information security requirements. It focuses on essential and important entities, which are legally required to meet elevated security standards.
The law aims to make the German state, economy and society more resilient to cybersecurity threats. It is intended to better protect companies against cyberattacks, system outages and other security-related incidents. At the same time, the law explicitly addresses supply chain risks and requires companies to conduct holistic risk management, extending beyond their own organizational boundaries.
The NIS2 Implementation Act came into effect as a federal German law on December 6, 2025. There are no general transition periods for affected companies – and the legal obligations set out in the law are now in full effect.
The affected companies must:
- register with the Federal Office for Information Security (BSI) by March 6, 2026,
- report significant security incidents to the BSI within the stipulated periods,
- implement appropriate technical and organizational security measures, and
- demonstrate compliance to the BSI (e.g. through reports, audits or certificates).
Whether companies are affected by the NIS2 Implementation Act depends on:
- the sector in which they operate and
- their size and economic significance.
The law particularly affects companies in the following sectors:
- Energy
- Transport
- Finance
- Health
- Water
- Digital infrastructure
- Space
- Postal and courier services
- Waste
- Chemicals
- Food
- Industry & production
- Digital services
- Research
Exemptions
Depending on their size and annual turnover, the NIS2 Implementation Act applies to companies that:
- perform a critical activity or an activity of systemic relevance,
- could have significant implications for public order or security, or
- are subject to systemic risks with the potential for cross-border impact.
At the same time, the law sets out very limited exceptions in which certain entities can be fully exempted from the scope of application. These exemptions are extremely specific and clearly defined in the law.
If a company is classified as a essential or important entity, it is now subject to binding legal obligations. These include:
Governance, organization and reporting
- Register with the Federal Office for Information Security (BSI)
- Designate and update contact partners
- Report significant security incidents to the BSI within the stipulated periods
- Demonstrate compliance to the BSI (e.g. reports, audits, certificates)
Risk management and security measures
- State-of-the-art technical and organizational measures (TOMs)
- A holistic, overarching risk management approach that takes account of IT systems, processes, components and the operating environment
- Risk analysis and information security guidelines
- Incident management: Preventing, identifying, managing and investigating security incidents
- Business continuity management (BCM): Back-up strategies, disaster recovery and crisis management • Supply chain security: Managing risks associated with service providers, partners and suppliers
- Secure procurement, development and maintenance: including vulnerability management and coordinated disclosure
- Regular assessment of security measures’ effectiveness
- Cyber hygiene and training for employees
- Cryptography and data encryption
- Personal and physical security: Access controls, authorization management and asset management
- Secure authentication and communication, e.g. multi-factor authentication and secured voice, video and data communication, incl. emergency communication
An exhaustive explanation of the context, insights, measures and recommendations can be found in our whitepaper: “Von der NIS2-Pflicht bis zur IT-Resilienz durch Künstliche Intelligenz” (From NIS2 obligation to IT resilience thanks to artificial intelligence). It features valuable expert tips and a fascinating interview on the topic of AI in cybersecurity.
Call on LHIND’s NIS Consulting and Expertise to Support Your Implementation
As specialists in IT consulting, system integration and innovative technologies, we have years of experience and in-depth expertise in the fields of IT security, data protection and compliance. Our customer base includes various companies from critical infrastructure (KRITIS) sectors with specific IT security requirements.
Our highly qualified IT experts have in-depth understanding and extensive experience of working with companies in many industries. This means they also have the expertise needed to perform the requisite process analyses and develop tailored solutions. Drawing on these capabilities, we would be happy to advise and support you in applying the precise requirements of the NIS2 Implementation Act in your company.
Ask us your questions about the NIS2 Implementation Act – and start your company’s journey to full NIS2 compliance!
We look forward to sharing our expertise insights.